ABOUT
US
We are a cybersecurity platform
for the operation of technological
risk management.
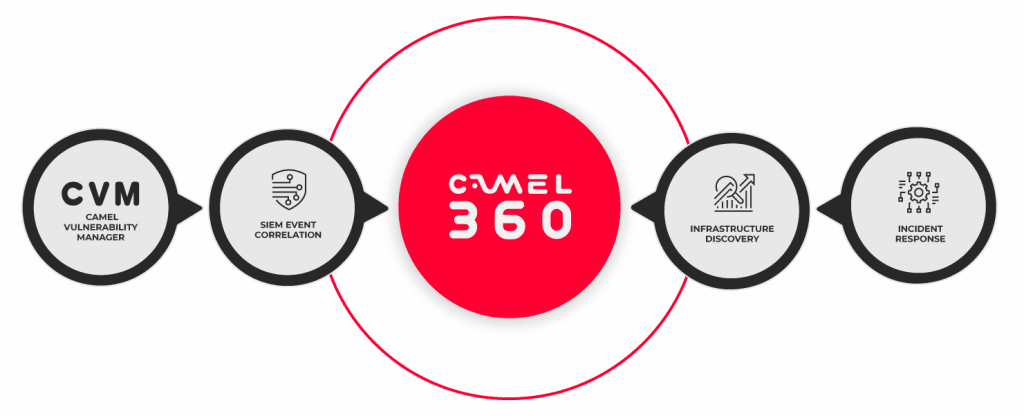
Multiple challenges, one solution
Camel Secure is the only cybersecurity suite that has all the necessary technology to accompany your operation and technology risk management process.
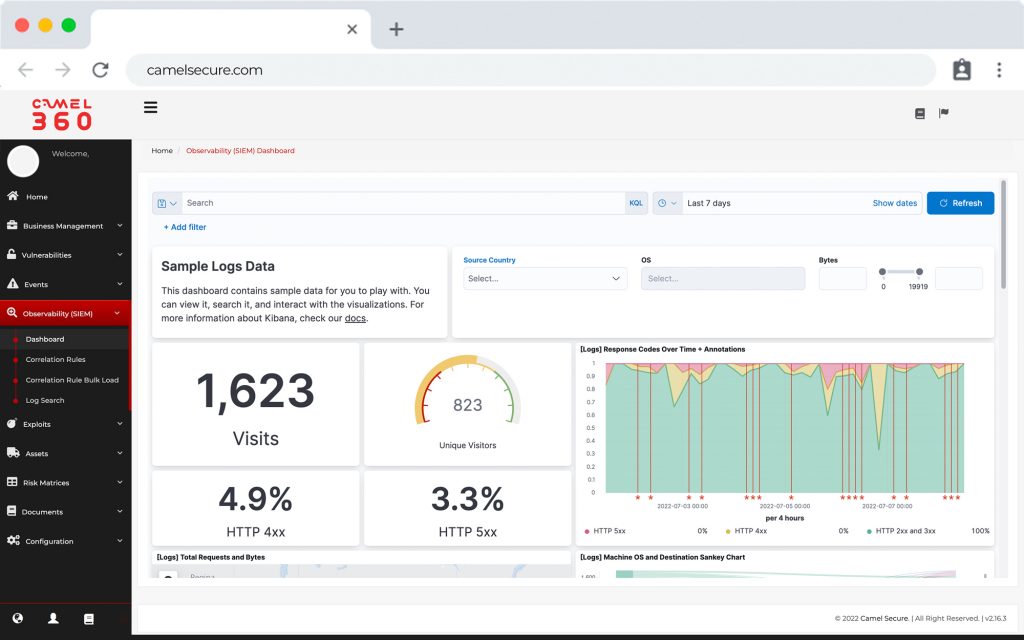
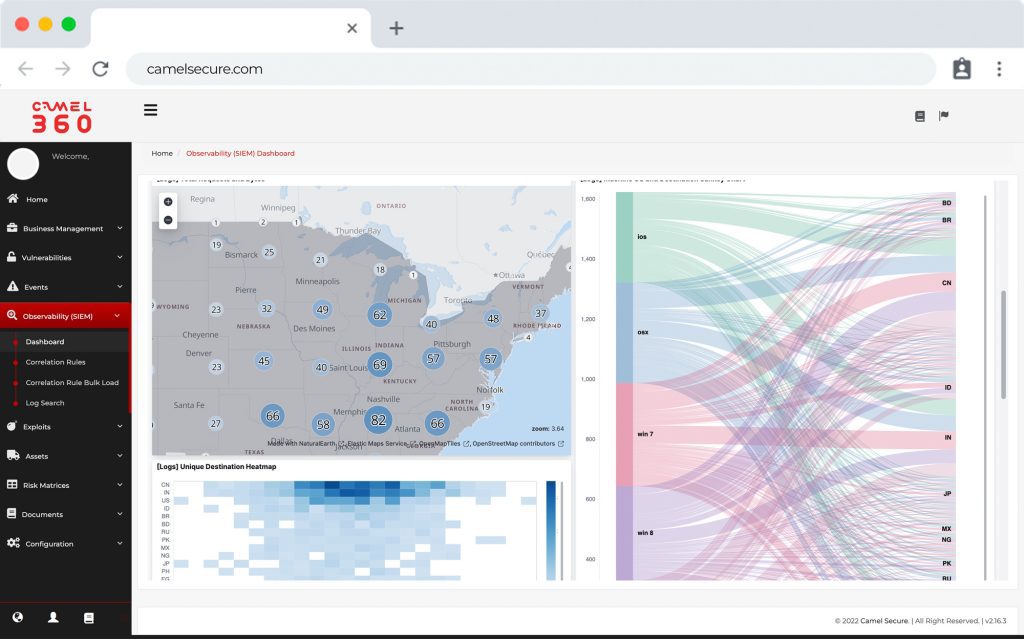
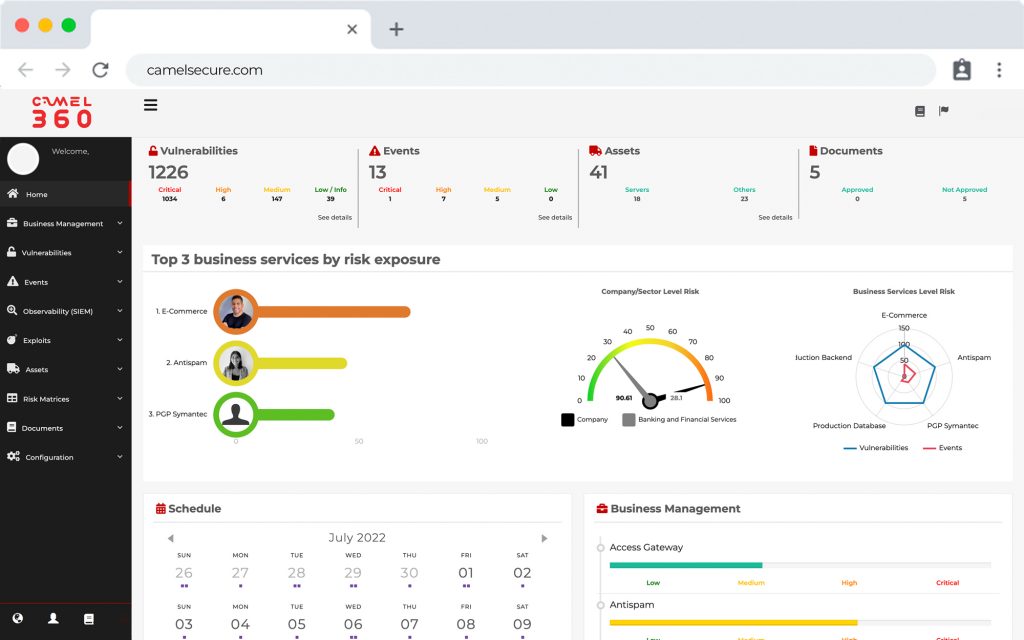
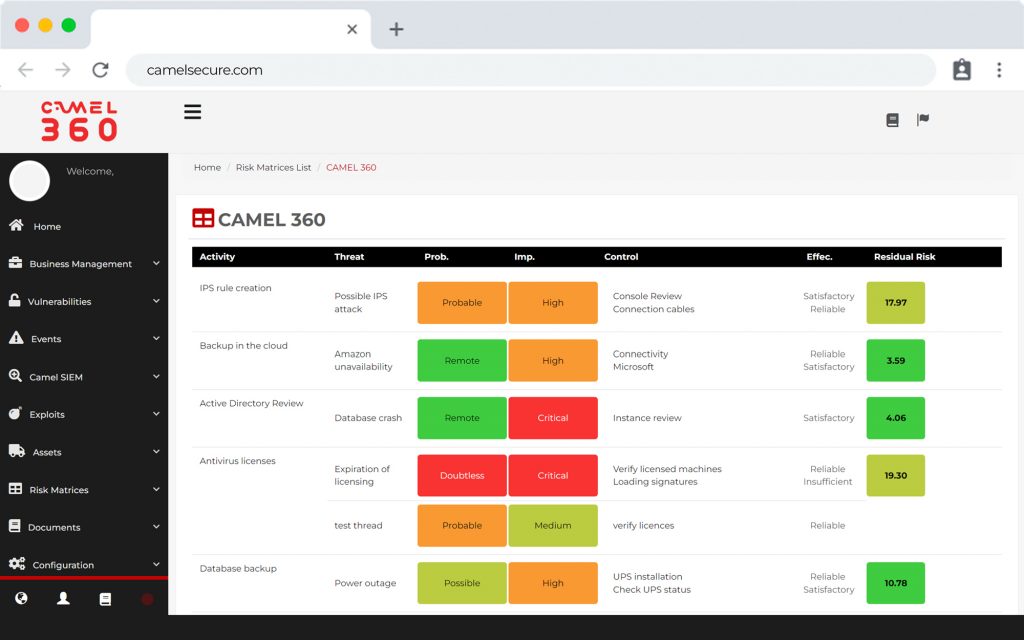
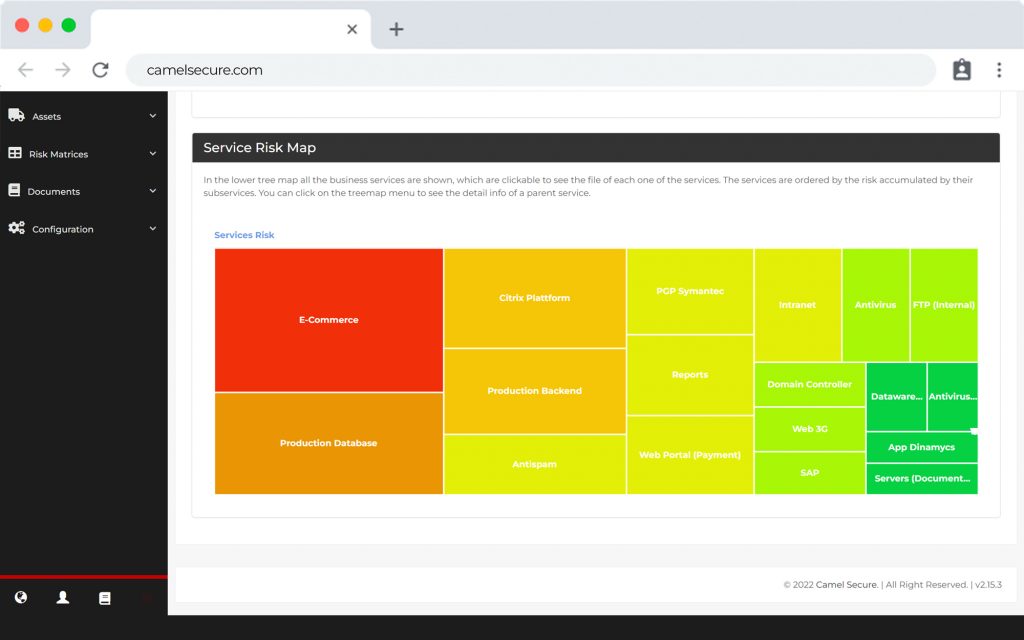
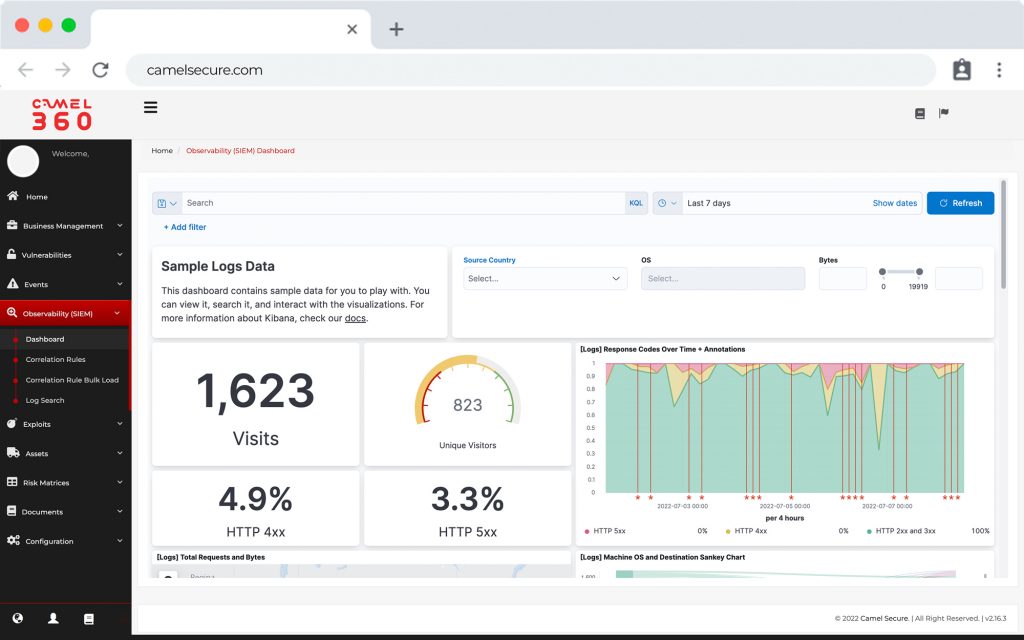
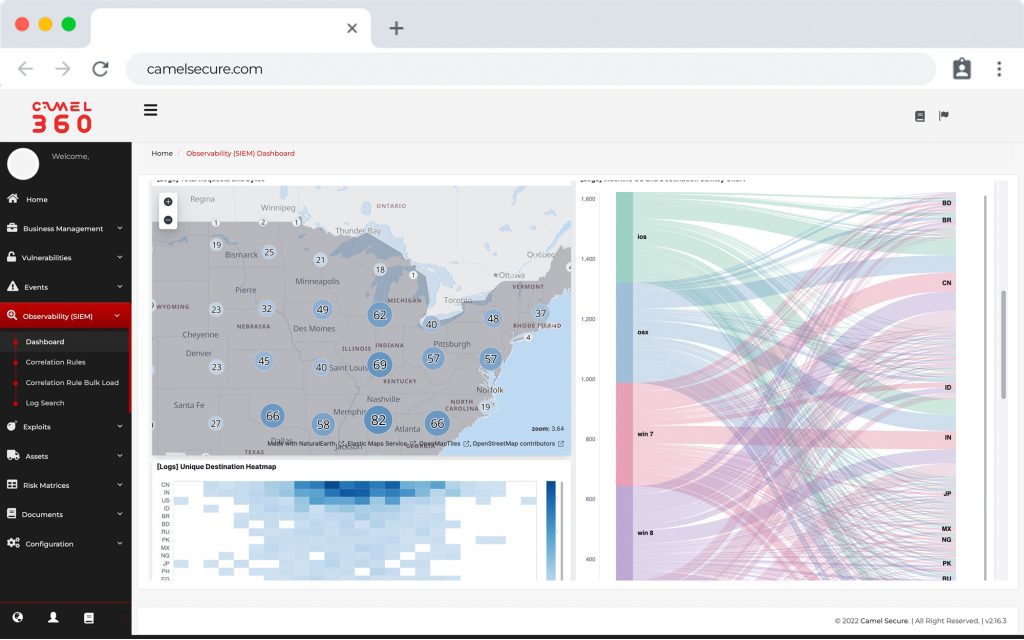
Among the functionalities of our platform are included: SIEM, Analysis and management of vulnerabilities operation, Management and calculation of IT risk, Library and discovery of assets, Heat maps or Risk Matrices.
All this in Service as a Service (SaaS) mode. This allows the necessary flexibility for rapid acquisition and implementation.
With the idea of changing the paradigm in which cybersecurity is a complex process that involves managing several platforms in parallel. Camel creates the vision of a single platform, which allows centralizing and correlating cybersecurity and compliance operations with a business-agnostic and fully agnostic view. Bringing IT closer to the “Business” operation.

We help companies to enter the world of cybersecurity and support their critical operations with our technology.
Camel working on











How does cyber intelligence work with Camel Secure?
We are so used to normalizing the complexity of cybersecurity, that sometimes we may be willing to disregard or outsource the responsibility of keeping our company secure. This allows the Business areas that are responsible for financially and operationally running the company to be completely separated from the technology areas.
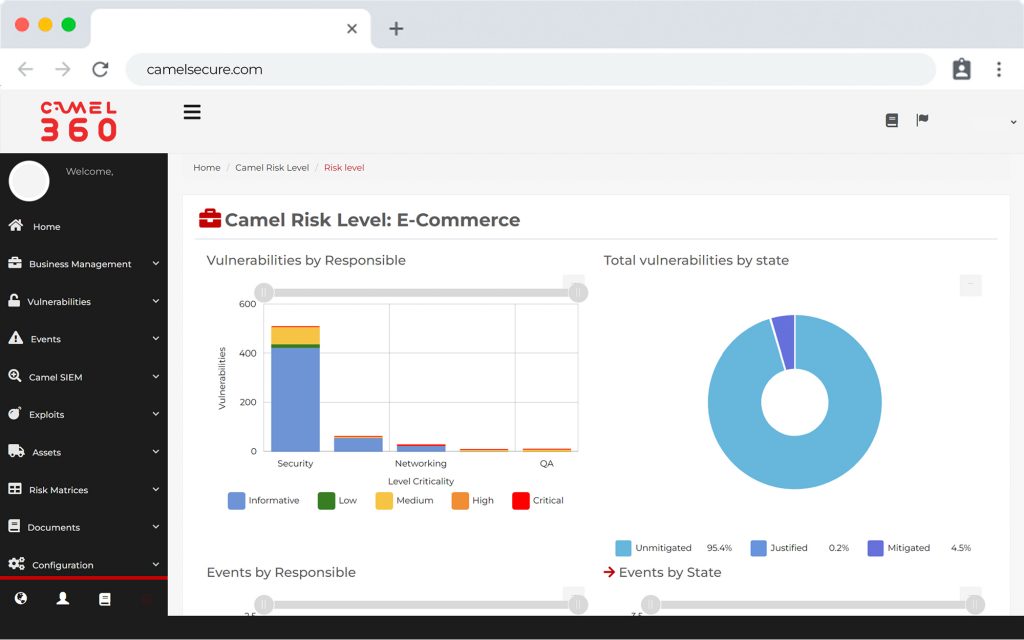
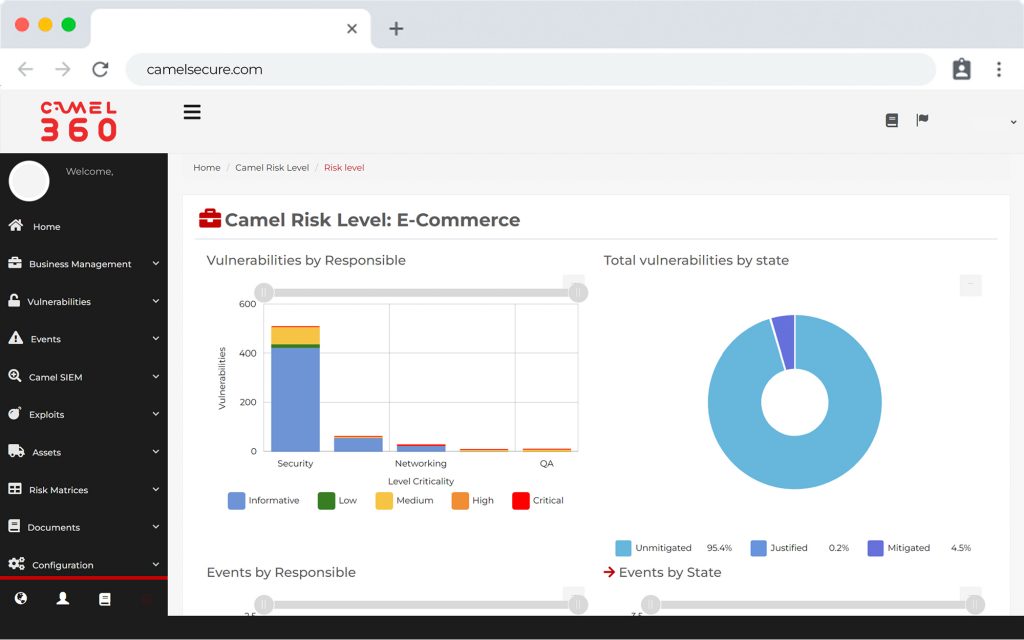
That’s why Camel can perfectly mimic the behavior of a human worker and help them execute complex, time-consuming tasks in just seconds. This information is then presented in intuitive operational dashboards close to the business, allowing the different areas of the company to be always informed of their cyber risks in order to make the best decisions.
What sets us apart?

Agile
Our solutions work in multi-processing, allowing the execution of several different processes at the same time. In addition to having the ability to configure the level of technical depth of learning, correlation or integration with other platforms.
Flexible
We create a platform that allows the enablement of functional modules in real time, thus adjusting to the reality of all our users, whether they are large, medium or small companies.
Scalable
We seek that our users can build and relate their critical services, from the simplicity of a machine, to complex developments involving large enterprise architectures.