Agenda una reunión con un especialista
At camel, we don't just help you with your technology challenges.
We eliminate them
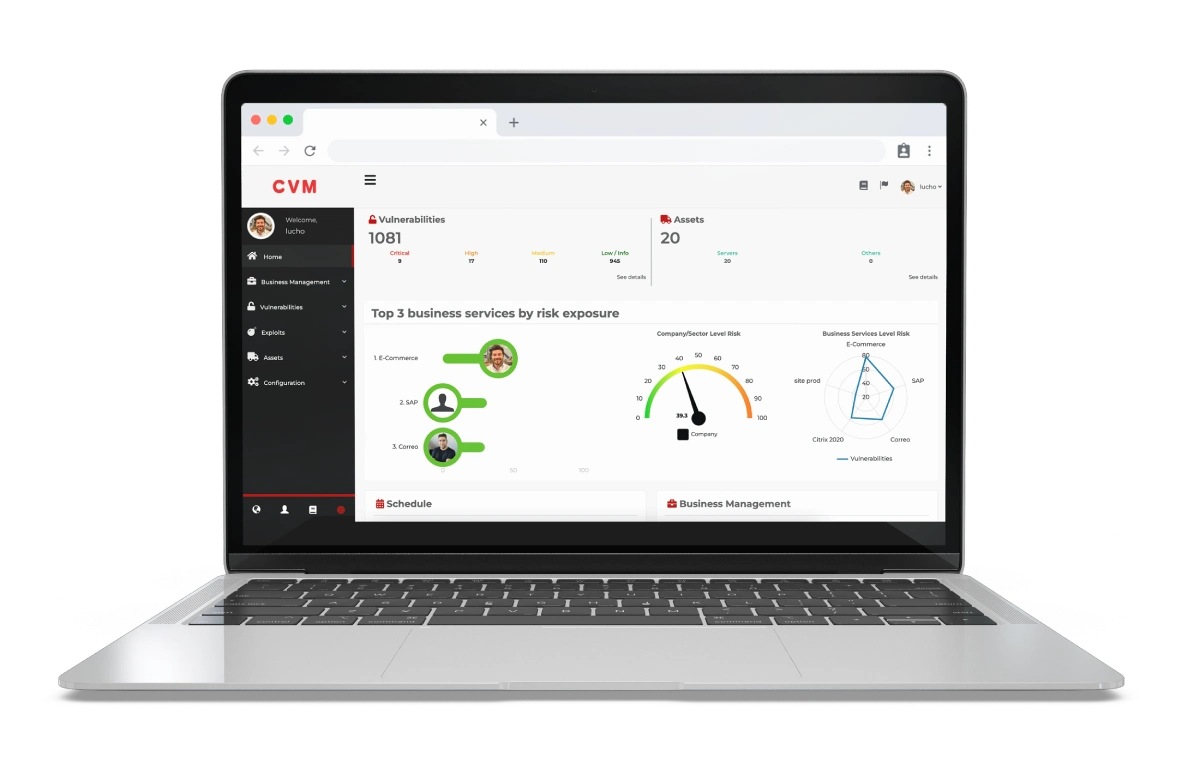
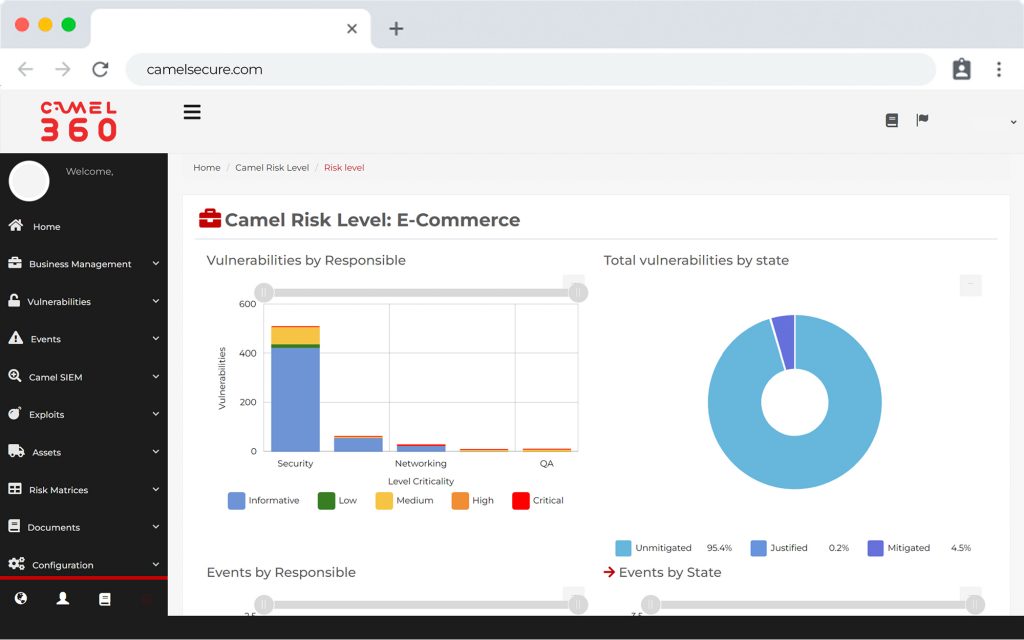
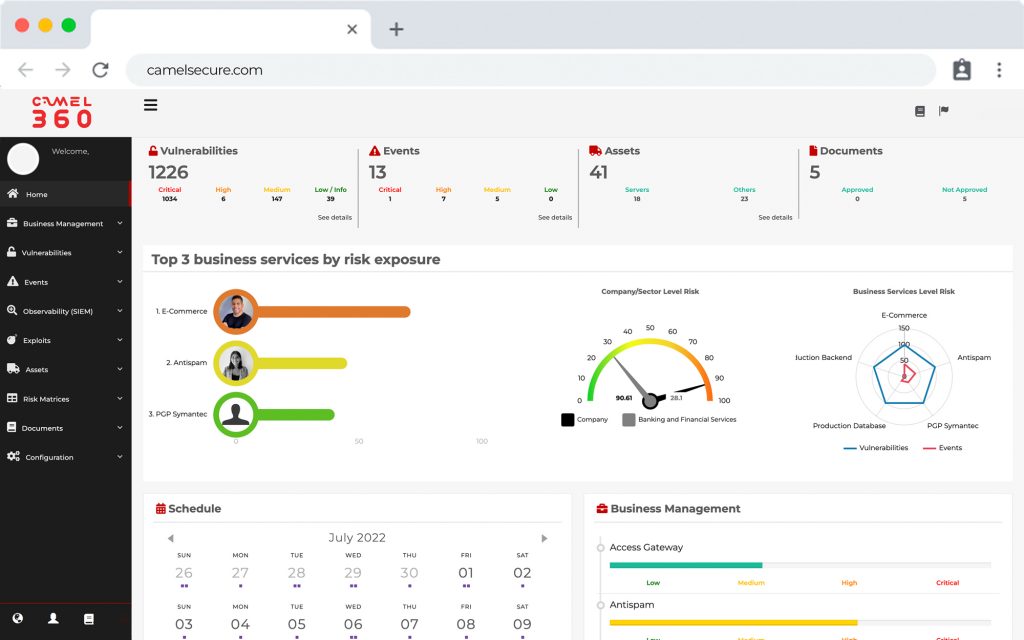
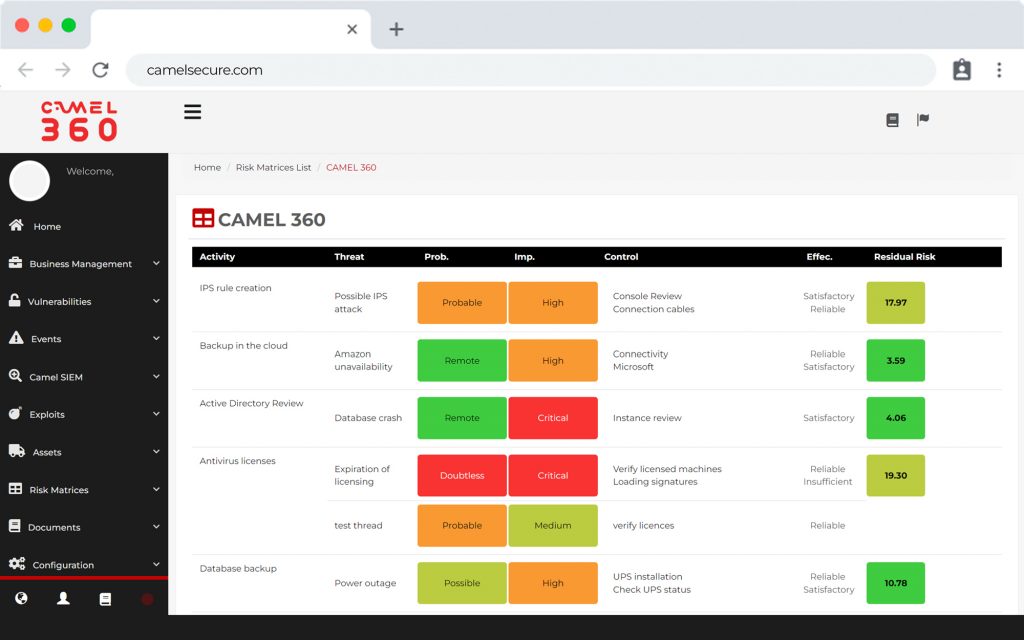
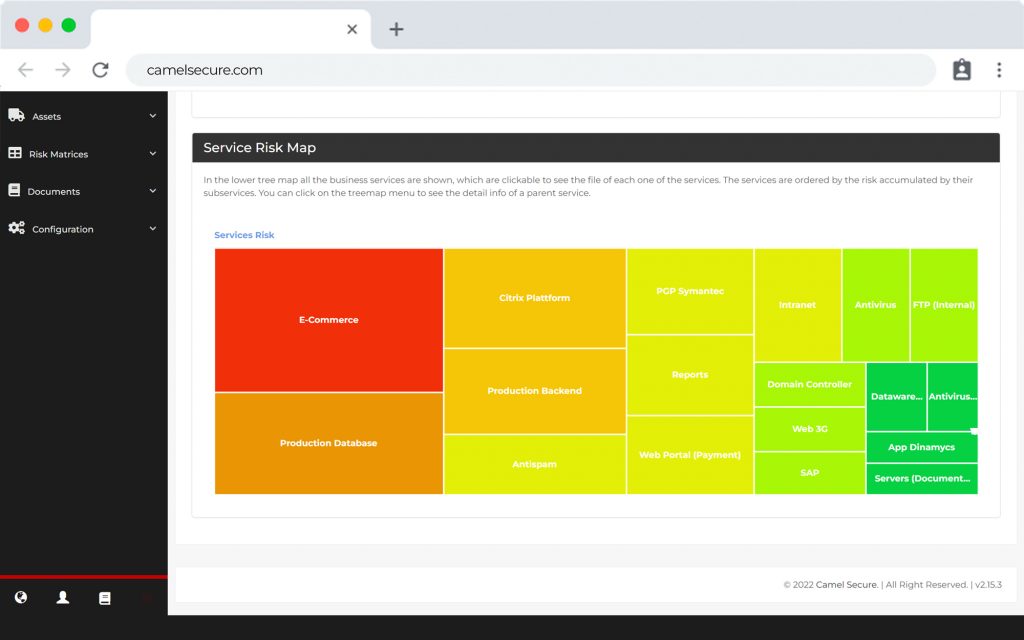
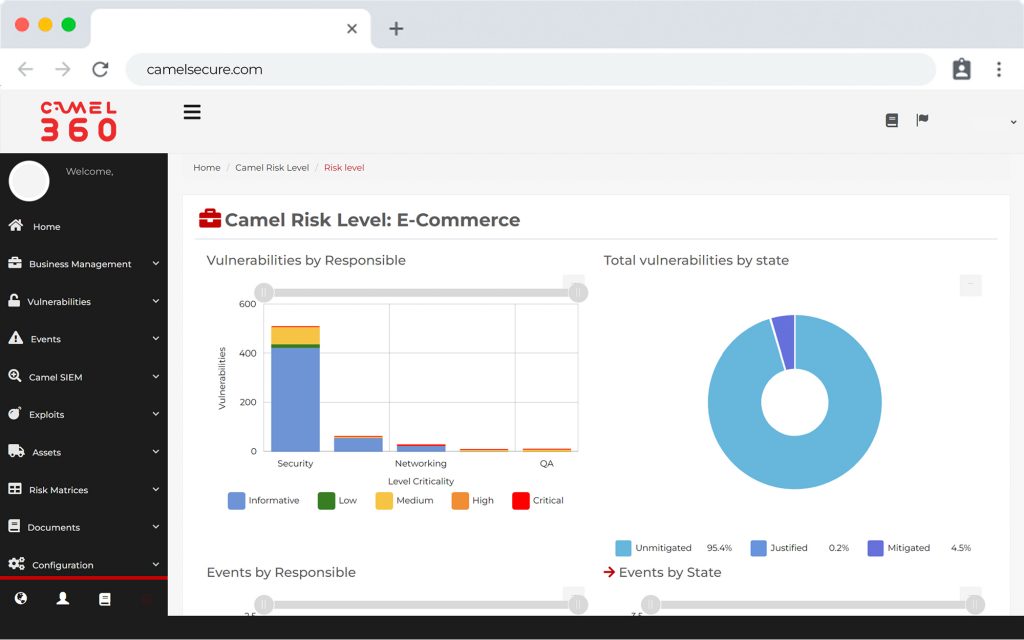
CVM brings together the functionalities of both Camel X (Infrastructure Vulnerability Scanner) and Camel W (Web Vulnerability Scanner), allowing to analyze IT vulnerabilities and web vulnerabilities but, in addition to that, it also gives a focus on the critical processes (or business services) of the organization, and allows to manage the vulnerabilities found within the same platform, assigning resolvers to groups and configuring SLAs. It also has the functionality to auto-discover and manage assets through its infrastructure library.
Create your own
library of
infrastructure
Now it's easy
CAMEL CVM has a multi-classification CMDB, which allows you to discover or create infrastructure assets with the particular configuration of each component and for each business.
ADVANCED CUSTOMIZATION
More automation,
less hassle
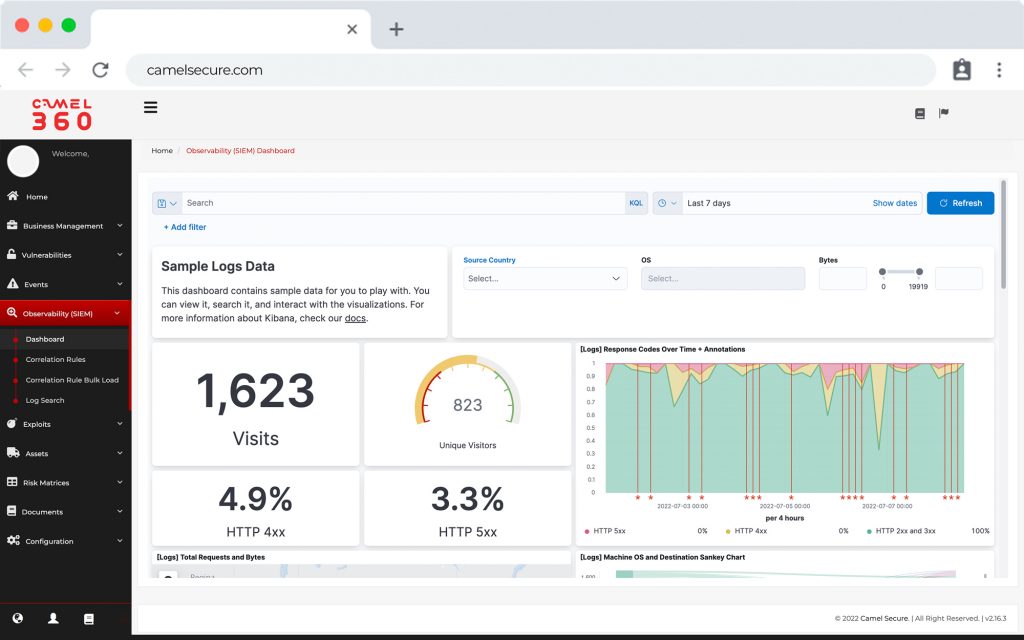
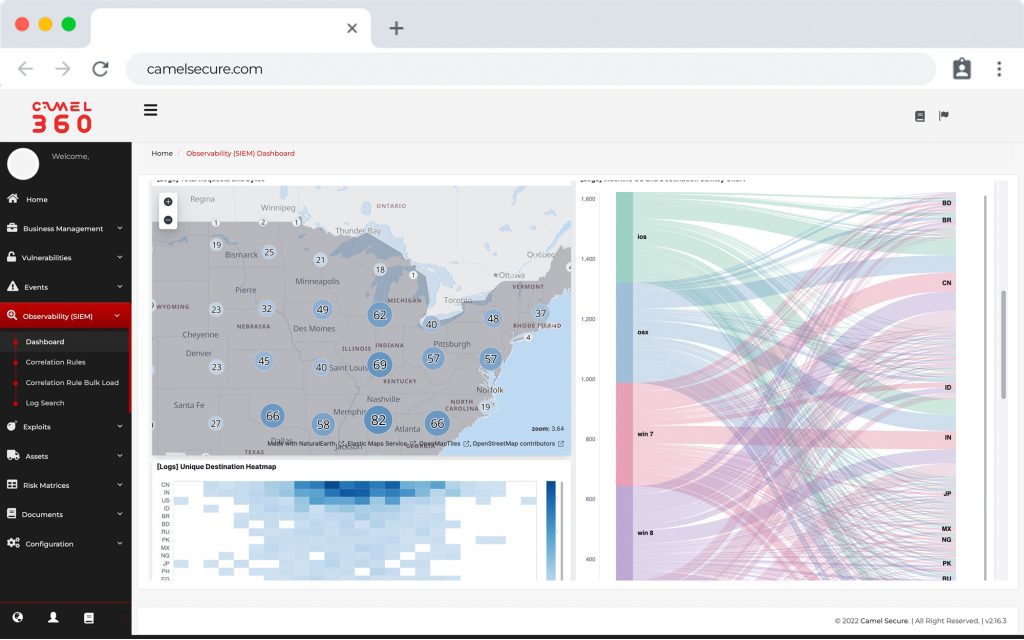
Allows access to the most advanced vulnerability scanning technology, with CAMEL CVM you can:
Schedule multiple scans
Vulnerability mapping by
technology or operating system
View operational and executive
Operational and executive dashboards
Artificial intelligence for
vulnerability
vulnerabilities according to OWASP
CAMEL CVM , a powerful tool and the most suitable one for organizations and security consultants
SUPPORT
ADVANCED
Access through our “CAMEL COMMUNITY” platform to our various professionals in the region, allowing queries related to CAMEL W or related products, such as CAMEL X, CAMEL WX or CAMEL 360, via forums, email, chat or telephone.
CAMEL CVM
IT'S AGNOSTIC
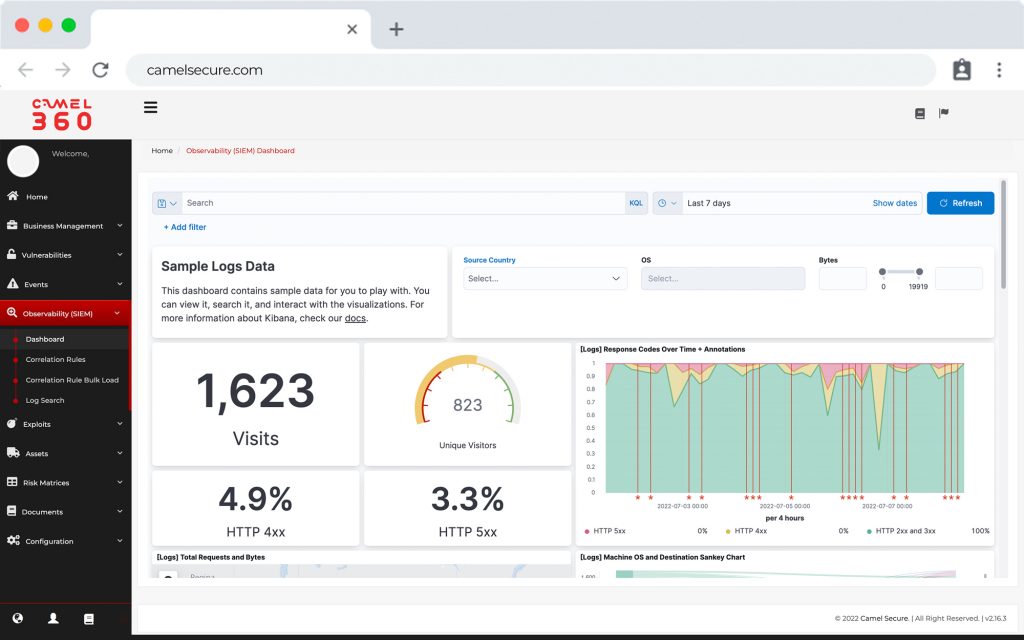
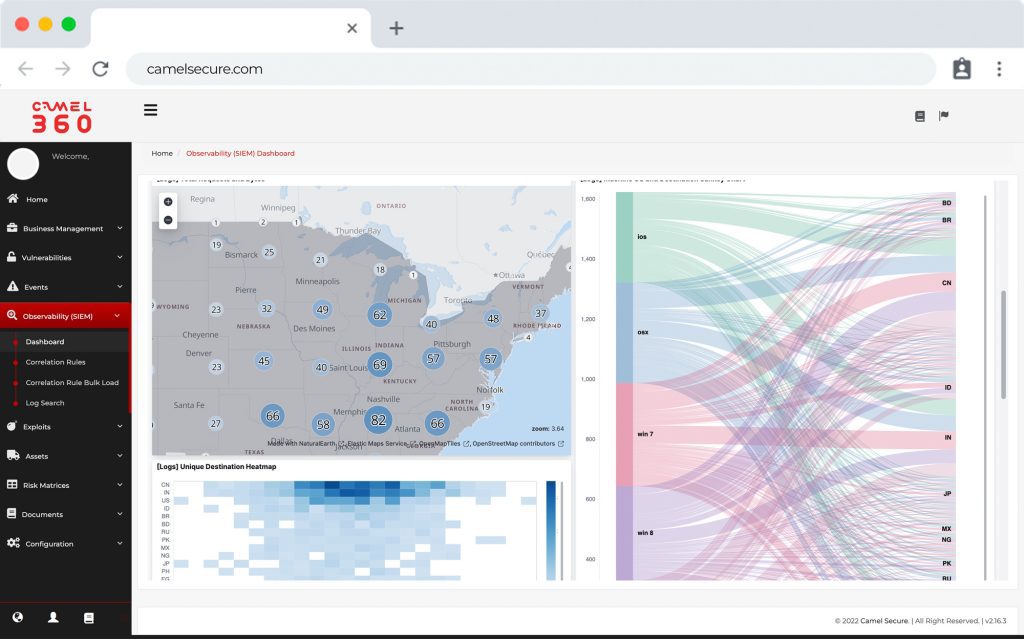
CAMEL CVM is the only Vulnerability Scanner that allows you to connect to other vulnerability scanning platforms and correlate your information on a single platform. This provides a holistic and historical view of the entire vulnerability scanning cycle, without having to use different platforms.
THE SECURITY
OF CAMEL
CAMEL CVM has the highest security standards, controlling end-to-end connectivity through SSL, AES-256 encryption, two-factor authentication, WAF, Security Group and controlled access lists.

Discover the
Camel's strength
Execution of unlimited SCANS
No limit to the number of assets in the CMDB
Your data is encrypted and your access is protected by two-factor authentication.